IGA is an essential part of your security strategy
IGA helps you to protect your valuable digital resources and data, comply with regulatory requirements, and manage user access efficiently. This reduces the risk of unauthorized access, data breaches and other security incidents.
Protect the keys to your digital kingdom with an IGA solution.
Protect the keys to your digital kingdom with an IGA solution.
Key components
Five key components of an IGA solution
Identity Lifecycle Management
This involves managing the creation, modification, and deletion of user accounts and their access privileges throughout their lifecycle. Access Governance
This includes defining and enforcing policies and controls for user access based on their job responsibilities, data sensitivity, and compliance requirements.
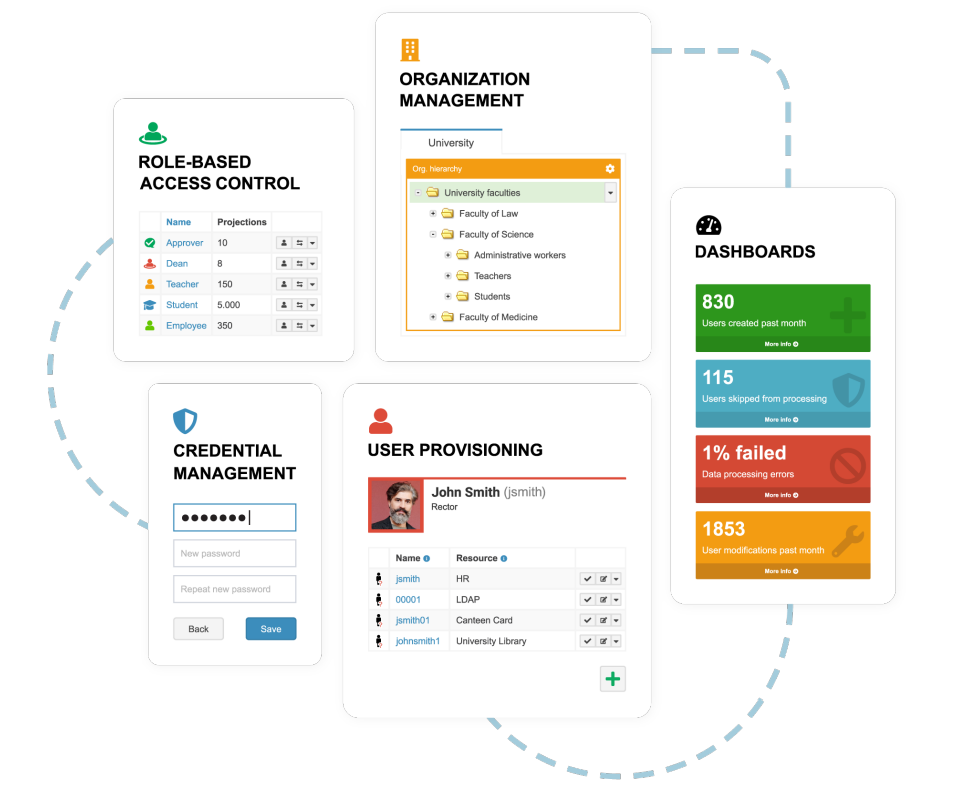
Role-Based Access Control
This relates to defining user roles and assigning access rights based on those roles, which simplifies access management and reduces the risk of unauthorized access.
Access Certification
This implies periodic review and certification of user access to ensure that access rights are up-to-date and comply with regulations and policies.
Identity Analytics
This involves analyzing user access patterns and behavior to identify potential security threats and compliance violations.
Why IGA
Four reasons for IGA
Security
IGA helps organizations ensure that access to their resources is limited to authorized personnel only. By maintaining an up-to-date inventory of user accounts and their access privileges, IGA can help prevent unauthorized access to sensitive data and systems.
Compliance
Many regulations and standards (such as HIPAA, PCI-DSS, and GDPR) require organizations to have proper controls in place to manage user access to sensitive information. IGA solutions can help organizations comply with these regulations by providing auditable records of user access and entitlements.
Efficiency
IGA solutions can automate many manual processes related to user account management, such as provisioning and deprovisioning of accounts, access requests, and certification of user access. This can help organizations reduce the workload on IT staff and improve the speed and accuracy of user account management.
Cost savings
By automating manual processes and reducing the risk of security breaches, IGA solutions can help organizations save money in the long run by avoiding the costs associated with security incidents, compliance violations, and manual labor.
Our expertise
Identity management solutions for companies of all sizes and all industries
+1.000.000
Provisioned identities
2007
our first year in identity management
+ 20
trained experts in our team

Identity Check up

Expert Services

Microsoft Azure AD

Operational Mentoring

Go-Live Support

SAP Integration

Setup Services

IAM Strategy Workshop Offering

Streamlined Application Onboarding

IGA Version Upgrade Services
Our ready-to-use prepackaged solutions
Ventum Plugin Library for SailPoint IdentityIQ
The Ventum team has created some IdentityIQ plugins that can save your time and improve your productivity.
Insights into our topics